I am going once again through data security training. That is not in itself bad, but the misguided and outdated recommendations propagate misinformation. Security is very important, but why can’t the “security” experts learn?
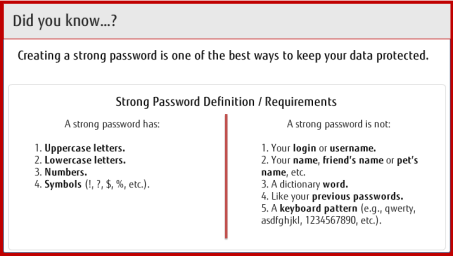
We are presented with this guidance:
The most important aspect of a strong password, is that it is easy to remember. When you have 30 to 40 passwords to use just for the official job functions (not counting all the personal online services) it can be a challenge to keep them all straight. A hard to remember password will be written down … because it is hard to remember. Duh!
Writing down passwords is a security flaw. Duh again!
Therefor, it is quite clear that for a strong password to be successfully used, it must be at the same time easy to remember. One can easily make a strong password that is easy to remember … without engaging in any of the prohibited actions mentioned on the right.
The strongest password you can create is a list of letters that correspond to a complete phrase that you are familiar with. Take a phrase that you know, but is obscure, probably something personal to you which you can easily remember, but nobody would necessarily know it is associated with you. For this example I am using a very popular phrase, but in real use you should not use a popular phrase.
“Now is the time for all good men to come to the aid of their country”
You password is the first letters of all the words: “nittfagmtcttaotc”
That is a strong password. Try it. If you know the phrase, it is easy to type. It essentially is a random collection of letters. It will be as hard for a password generator to guess as any password.
It is even better if you are a little less regular about this and mix up the letters that you transform to. One recommendation I saw was the phrase “This little piggy went to market” might become “tlpWENT2m”. Another suggested the phrase might be “Try to crack my latest password, all you hackers” to become “t2cmlp,@yh”.
You can have the strongest password in the world, but if you have to write it down, then all advantages of a strong password are lost.
Why do these “security recommendations” ignore the fact that human factors is the single largest cause of unauthorized access? There is some evidence that the cryptic hard to remember passwords are actually worse than simpler, but longer phrases. NIST guidelines recommends that people create long passphrases instead of gobbldegook short passwords.
It continues with this page:
 What is missing? Usability. Again, you can make a super secure system, but if it is extremely difficult to use, then there is a strong disincentive to use it.
What is missing? Usability. Again, you can make a super secure system, but if it is extremely difficult to use, then there is a strong disincentive to use it.
For example, in Windows one can control the access of every document down to exactly which users can read or update. But almost business user today ever uses it! It is too tedious. Sometimes, on a network drive, one might set the access to a complete folder to a group or something, but that leaves the door open for a wide variety of people. This is not really Microsoft’s fault: it is that the paradigm of setting up specific users access to specific files is just inherently tedious.
The most important aspect of a security system is that a regular business user can easily navigate the controls to accurately and easily restrict access from the right people, and allow access to the right people.
Part of a good usable system will be indicators that tell you when it is wrong and help you get around it. For example, when a user should have access, and doesn’t, there should be an easy way to request and get access — without a lot of tedium. The access control should be easily visible.
When there is a failure of security or a mis-configuration there should be a clear error message that accurately tells what was restricted and why. Most primitive security people believe that no error should be produced, or if one is, there should be no discernible information in it. All of this makes most data security environment so difficult to use that people avoid it.
Eventually I encounter this screen in the training:
 The checked answer is the one you must choose to get the question correct.
The checked answer is the one you must choose to get the question correct.
I had thought the security experts were simply oblivious to usability concerns, but it seems that they are actively against having passwords that are easy to remember! They actually believe that having a hard to remember password is better security! Unbelievable! It can be a big challenge to remember 30 to 40 password just for the job, all of which are expected to be different and changed reasonably often.
Yes, I know, password managers like LastPass do a good job of solving this memory problem. Very convenient. The clear advantage is that you can have super strong passwords, as long as you want, and change them as often as you want. I used it for a while, but I had some problems with it inserting itself into all the web pages I browsed. I don’t remember exactly the problem, but I had to stop using it.
Again, an easily remembered password will not be written down, and therefor will be safer and more secure.
Super Ironic
The email telling me about the security course has my username and password (for the course) directly in the email. Yes, I know this is not a super-secure bit of information, but if you want to train people to behave the right way, it would make sense to demonstrate the correct behavior even when it is not necessary. It is particularly ironic that a training class on security uses a bad security shortcut itself.
Why do they do that? It is too difficult otherwise! They found people failed to do the course when they had to set up and maintain their (separate) password for the course. Hello? Is anyone listening?
Another course
I got done with another course, and the last step of that course was to fill in a survey. I linked to the appropriate page, Logged in carefully. The instructions said to press a button to fill in the survey. This is what was presented to me:
 Is it access control gone wrong? Maybe. Probably. The people who made the survey probably have no idea this is happening. Usability is strictly a secondary consideration around security access problems.
Is it access control gone wrong? Maybe. Probably. The people who made the survey probably have no idea this is happening. Usability is strictly a secondary consideration around security access problems.
I am not the only one feeling this way
- The Guy Who Invented Those Annoying Password Rules Now Regrets Wasting Your Time
- Classic XKCD Comic on password selection.
- The Common Mistakes That Make Your “Strong” Passwords Weak
- NIST update: Passphrases In, Complex Passwords Out
- NIST document SP 800-63B: Authentication & Lifecycle Management (pdf)
- Passwords Are Not Broken, but How We Choose them Sure Is
- NIST: Easy Ways to Build a Better P@$$w0rd

Pingback: CIA triad: Warranty vs. Utility | Jacob Ukelson's Blog
Rookie receveur Kelvin Benjamin a été un grand plus avec une équipe de pointe de 999 verges et neuf touchés.